 The Remote Desktop Protocol (RDP) is a secure network communication protocol tailored to remote management, remote access to virtual desktops and applications, and for the RDP Terminal Server.
The Remote Desktop Protocol (RDP) is a secure network communication protocol tailored to remote management, remote access to virtual desktops and applications, and for the RDP Terminal Server.
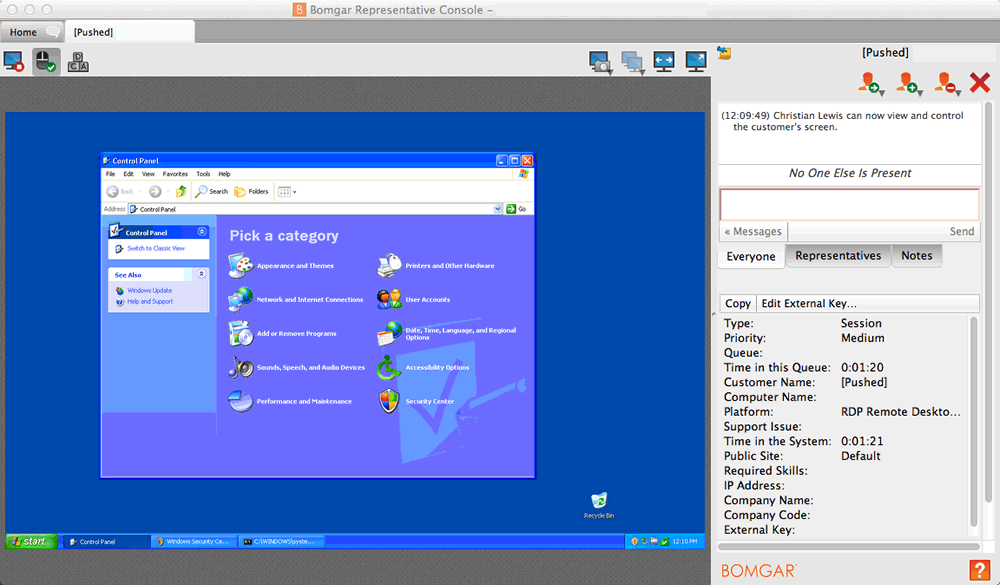
RDP allows administrators to remotely diagnose and resolve individual user and system problems.RDP is available for most versions of the Windowsoperating system. Another option is the RDP for Apple’s macOS. In addition, there is also an open-source version of the protocol.
How the Remote Desktop Protocol works
The RDP protocol provides remote access over the TCP/IP on port 3389. An RDP-enabled application or an RDP-capable service packs the data to be transmitted and the Microsoft Communications Service delivers that data to an RDP channel. From there, the operating system encrypts the RDP data and adds it to a frame so that it can be transmitted.
All RDP protocol activity is inherited from the Terminal Server Device Redirector Driver (RDPDR). This driver consists of subcomponents such as the RDP driver (Wdtshare.sys), which handles user interfaces, transfers, encryption, compression, and framing. The transport driver (Tdtcp.sys) is responsible for packaging the protocol for sending over a TCP / IP network.
Features
Notable features of the RDP include encryption, smart card authentication, bandwidth throttling, resource sharing, the ability to use multiple displays, and the ability to temporarily disconnect without logging out. RDP also allows the redirection of audio and printer functions.
RDP can use up to 64,000 independent channels for data transmission. Data can be encrypted with 128 bits and the bandwidth reduction optimizes the data transfer rate for slow data transfers.
Security in RDP
Despite all this, the protocol has also been struggling with security issues in the past. First versions revealed a vulnerability to man-in-the-middle attacks on the RDP session. This allowed attackers to gain unauthorized access.
Newer versions of RDP are more secure. When you buy RDP, consider it on a trustable platform because the newer Windows operating systems include a mechanism for determining which users can access the system through an RDP session. There is also an option to prevent someone from remotely accessing the system unless it uses network-level authentication.
It is generally recommended that administrators and end-users use RDP only when absolutely necessary and that they are running at the lowest possible privilege level.


